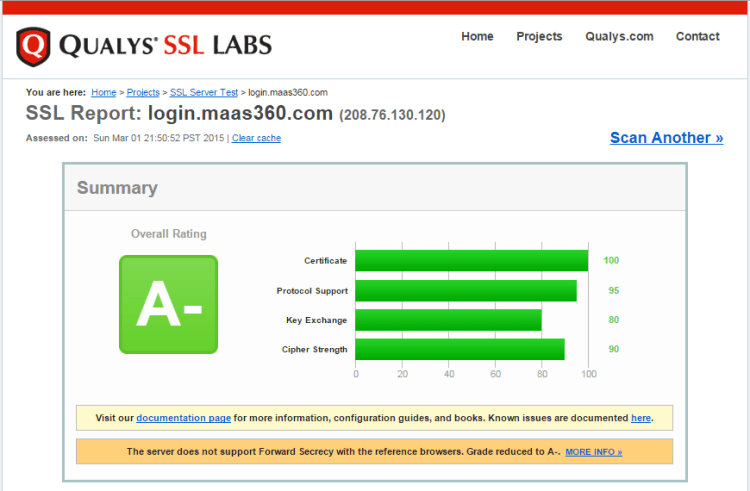
Earlier this morning I was chatting with a CIO of a large manufacturing organization with presence across multiple continents. They are currently benchmarking Mobile Device Management (MDM) vendors to help secure their mobile environment and we are helping them with this activity. As part of our rigorous methodology, we put 5 key vendors – Mass360 (owned by IBM), MobileIron, Good, Microsoft InTune and AirWatch (owned by VMware) – through the Poodle Attack Vulnerability check and results were amusing. While all vendors passed this test, AirWatch couldn’t make it to the finish line and got an overall rating of F. See pictures below for more details. We had reported another similar test last week where we found Microsoft’s Office365 vulnerable to the Poodle Attack.
The Vendors Who Passed The Test
The Vendor Who Didn’t Make It – AirWatch (owned by VMware) Failed The Test With an Overall Rating of F.
Greyhound Standpoint
Greyhound Research believes it’s an absolute must for organizations to have such security checks as part of the overall methodology to benchmark the Enterprise Mobility Management (EMM) players and other Cloud Service providers. The Poodle Attack is a critical vulnerability and IT Decision Makers must ensure all the shortlisted vendors pass this test.
What’s your Standpoint?
Are you currently evaluating/using Mobile Device Management as part of your broader Enterprise Mobility Management strategy and unsure about your current setup in light of these results? If you are a key IT decision maker in your organization and need guidance on devising a cloud security strategy best fit for your organization, leave a comment or send me an email on sgogia@greyhoundgroup.com.
Note for Technology Users – Join Our Exclusive Community!
Greyhound Research values your opinion and invites IT decision makers and business leaders involved in IT projects to join our exclusive, vendor-free research panel, Greyhound Golden Gate. If your story if exclusive and we have your permission, we will write a post about you and the project to share it with the larger community. Over and beyond, this also gives you access to some of our thought-leading research and experts. Please write to me on sgogia@greyhoundgroup.com and we’ll take it further from there!
Note for Vendors and Providers – Did you see our Research Agenda?
Do check out our extensive research schedule that covers a vast variety of topics including new-age business themes, disruptive technologies, business and technology roles. Please write to me on sgogia@greyhoundgroup.com and we’ll gladly share a copy of the research schedule with you.
Related Material On This Topic
- CIOs Need A Broad Outlook For Developing Security Strategies
- The Cons Of Microsoft Office 365
- Enterprise Mobility – Value Lies in Data, Not Device Alone!
Wish To Use This Material?
Greyhound Research is happy to provide reprint rights and official reprints in PDF format. Please send us a note on connect@greyhoundgroup.com.
Copyright © 2015 Greyhound Research. All rights reserved.
 About The Author: Sanchit Vir Gogia is the Chief Analyst & CEO of Greyhound Research, an independent IT & Telecom Research & Advisory firm. He also serves as Founder & CEO of Greyhound Knowledge Group that operates under four brands – Greyhound Research, Greyhound Sculpt, Greyhound Technocrat and Greyhound Vivo. To read more about him, click here.
About The Author: Sanchit Vir Gogia is the Chief Analyst & CEO of Greyhound Research, an independent IT & Telecom Research & Advisory firm. He also serves as Founder & CEO of Greyhound Knowledge Group that operates under four brands – Greyhound Research, Greyhound Sculpt, Greyhound Technocrat and Greyhound Vivo. To read more about him, click here.
Discover more from Greyhound Research
Subscribe to get the latest posts sent to your email.






Reality it that Airwatch didn’t care about the Poodle vulnerability for a VERY long time and many of its servers remained vulnerable to this. The worst part of this fiasco is that they didn’t tell their existing customers that the Cloud that they were using was vulnerable. #epic #fail